With many companies and organisations still feeling the fallout of the recent WannaCry cyber-attack, IT automation specialist PowerON, has launched a number of free software solutions for companies and IT managers that were affected or are concerned by the attack.
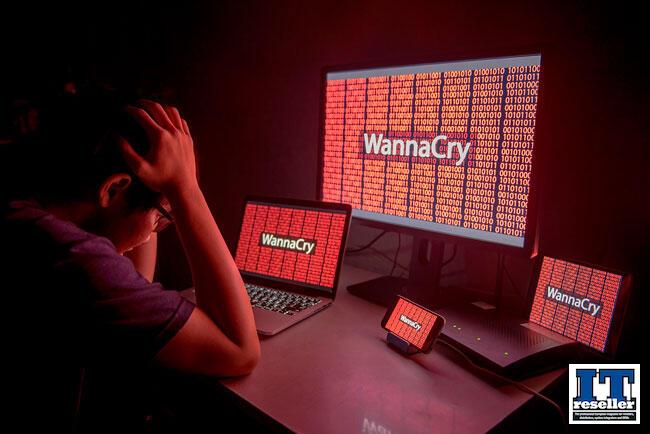
WannaCry struck a wide range of organisations and businesses across more than 150 countries including a number of NHS Trusts, along with the likes of Nissan and Telefonica. The ransomware encrypted data on victims' computers and demanded a bitcoin payment in return for restoring the files, with the ransom amount then increasing. The attack hit Microsoft machines primarily running Windows 7 and Windows Server 2008 R2 however, all versions from XP to Windows 10 and Server 2003 to 2016 are potentially vulnerable to the exploit used.
In response, PowerON has made a number of its software solutions, that are usually chargeable, free to download, as well as creating several additional downloads to protect those who haven't been attacked to ensure they remain secure.
Steve Beaumont, who is a Microsoft Most Valuable Professional and the Product Development Director at PowerON, explains: "Although WannaCry is no longer making the news headlines, it certainly hasn't just gone away. There are still reports of legacy systems falling victim to it and similar exploits, and we know there are huge numbers of computers and devices throughout the world that are infected with WannaCry, without their users even realising it yet.
"Microsoft has taken steps to fix these problems, and released new security updates that all users should be patching on a regular basis, which can be done using Microsoft's automated updates system. However, we now have the possibility that different variants of the malware are being developed by attackers. As a result, we've made PowerON's Infrastructure Management services deployable immediately, and free of charge for 60 days, which gives people a highly effective shield for a couple of months whilst they make sure their systems are fully secure and up to scratch."
Finally, Steve adds: "The stark reality is that the WannaCry cyber-attack could have been avoided, or at least had its impact greatly reduced, if customers had up to date patching, had not been running SMB1 (Sever Message Block) on devices, which is a sharing protocol meant for sharing files and printers between computers, and not allowing access to SMB from the internet. All Microsoft users should check these points on their computers, or ask their IT managers to do it, as an immediate precaution."

Add a Comment
No messages on this article yet